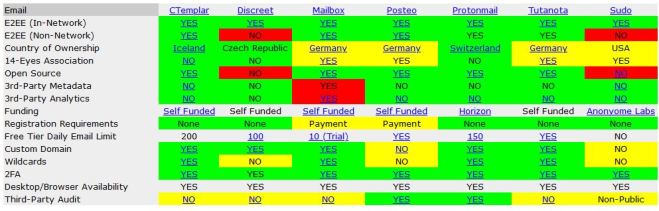
IntelTechniques has a chart they put out last month covering the security of voice, email, messaging, and video applications. Click here to view the page. Some explanations of the terminology used:
E2EE – end to end encryption. E2EE is good to have. If something is encrypted, but not end to end, then at some point in the data’s journey between two end points it is “in the clear” for anyone to view.
Country of ownership is there to indicate the likely laws governing privacy or to investigate how easily a company submits to subpoenas for access to their servers.
14-eyes association is another name for SIGINT Seniors Europe or SSEUR – an association of fourteen countries around the world who all share surveillance data with each other. For example, the US may have a law that makes it illegal to collect surveillance data on a US citizen without a warrant, but they can ask an ally from SSEUR to share that same data with them because it wasn’t collected by the US agency.
Open Source is the name for software where the program source code is available to the public to check (and even modify under conditions of the various open source licenses) for accuracy, security, or other reasons.
Third-party metadata – does the application allow metadata access (such as To, From, Subject, source IP, etc) to any third parties?
Third-party analystics – does the application allow any third party to analyze traffic that passes through the application system?
Ephemeral messages – An ephemeral message is one that can or will disappear from both the sender and receiver devices after some amount of time.
Third-party audit indicated whether the application source code has been audited by a neutral third party for security problems.
I believe that most of the other terms are more easily understood.
